CSRF Email Confirmation Vulnerability for Gmail & G-Suite in Facebook
This post is about an bug that i found on Facebook which used to verify any new Gmail and G-Suite account with minimal Victim’s interaction.

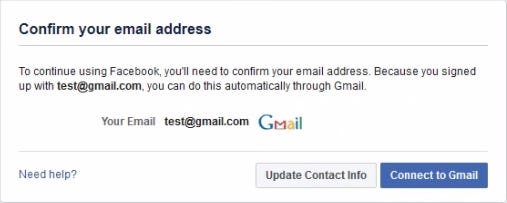
When a user create a new Facebook account with Gmail they can confirm the account with two methods.
- Confirming by entering 5 digit confirmation code
- confirming by OAuth login.
Method 1 is hard to bypass. because there is a rate limit for confirmation code. even though we try to brute force Facebook will block your account with Checkpoint block due to suspicious activity.
So i tried with method 2 . while testing i found a bug in OAuth login Flow.that the CSRF token validation was missing.
https://accounts.google.com/o/oauth2/auth?client_id=15057814354-80cg059cn49j6kmhhkjam4b00on1gb2n.apps.googleusercontent.com&state=ARf8Zzq50032sck96TSFssFhWVvMUWO7KEJlq3n3_7Yp73WcWvlpyFn1dpdoUGv5QOLAn2ffrRZ_L_3ZfAncV_I0Ihog80LabpToEfHUIgfzBK720-pGRNbXGeYkETOwjeCfbsl70shdjuLnp3jC4dIsn-xPTwoggineLFh34F61bbYGsg&response_type=code&redirect_uri=https%3A%2F%2Fwww.facebook.com%2Foauth2%2Fredirect%2F&scope=openid+email&login_hint=victim_email@gmail.comThe state parameter is a CSRF token. which will validate the request and response.
Example:
If a state parameter is generated in Firefox browser . then it should work only on same browser where it generated.
but in this endpoint proper validation was missing. and the same CSRF token can be used in any browser . so the Attacker can easily embedded the URL in web page and once victim click the link the victim email will be confirmed in attackers account.
but there is one problem . before clicking the link the attackers account should be logged into victims browser. in Facebook there are some one-tap login URLs.
i used this link. once the malicious page loaded . the link will get loaded in IFrame. and attacker account will get logged into victim browser.
https://www.facebook.com/recover/password/?u=<UID>&n=<6Digit code>&ars=one_click_login&fl=one_click_login&spc=1&ocl=1&sih=0Once the OAuth popup loaded the victim email will get confirmed. and once the popup closed the attacker account will get logged out using the below logout emdpoint.
https://m.facebook.com/logout.php?h=17AfealsadvYomDSSo by combining all this process with one web page. the attacker account will logged into victim browser and after confirmation the account will get logged out.
Video POC:
Timeline:
10-May-2019 : Report Sent
17-May-2019 : Further investigation by Facebook
31-May-2019: Fixed by Facebook
19-June-2019 : $3,000 bounty awarded by Facebook
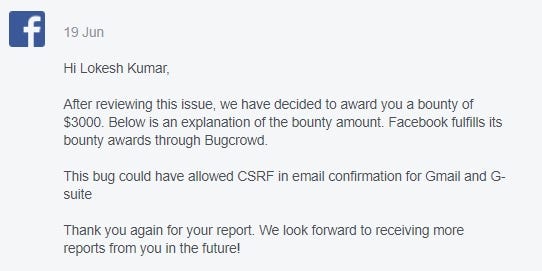
I would like to thanks Facebook Security Team for this Bounty

